It’s all concerning the information.
One factor is evident: the enterprise worth of knowledge continues to develop, making it a financial institution’s major piece of mental property.

From a cyber threat perspective, assaults on information are probably the most distinguished risk to banks.
Regulators, cyber insurance coverage companies and auditors are paying a lot nearer consideration to the integrity, resilience and recoverability of banks’ information — in addition to the IT infrastructure and programs that retailer the information.
So, what does this imply for the safety of enterprise storage and backup programs?
Just some years in the past, nearly no banking chief data safety officer (CISO) thought that storage and backups had been vital. That’s now not the case in the present day.
Ransomware has pushed backup and restoration again onto the IT and company agenda.
Ransomware teams reminiscent of Conti, Hive and REvil are actively focusing on enterprise storage and backup programs to stop banks from recovering their information.
These attackers understand that an assault on storage or backup programs is the one greatest figuring out issue to indicate if the financial institution pays the ransom. This has pressured banks to look once more at potential holes of their security nets by reviewing their storage, backup and information restoration methods.
Storage and backup safety in monetary companies
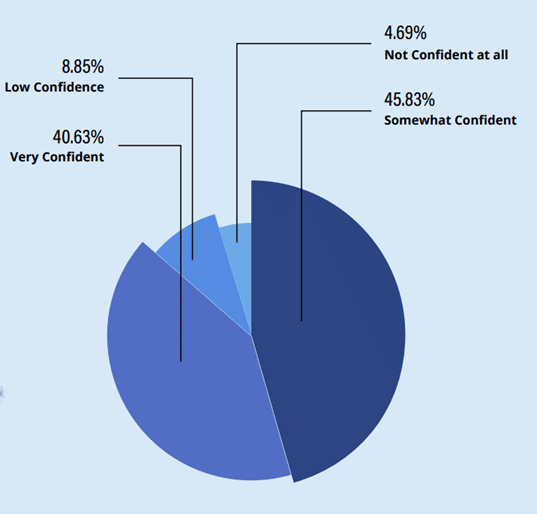
Continuity revealed a analysis report on the finish of final yr during which we surveyed 200 infosec leaders inside the banking and monetary companies sector. One of the crucial alarming findings was that just about 60% of respondents usually are not assured of their means to get well from a ransomware assault.
There’s clearly a recognition that as an trade, we have now safety blind spots.
With no sound storage, backup and restoration technique, corporations have little probability of surviving a ransomware assault, even when they do find yourself paying the ransom.
The banking sector is among the most closely regulated industries. Audits are carried out each internally and externally and have a tendency to evolve yr over yr primarily based on advances in know-how, trade regulation adjustments and shifts within the risk panorama.
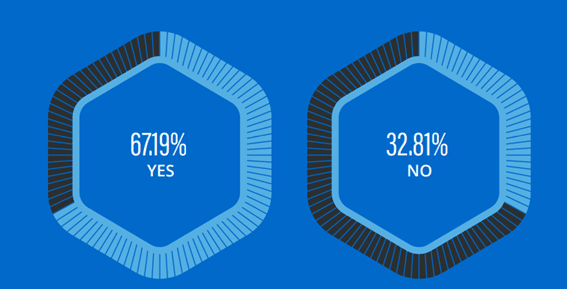
It was attention-grabbing to learn the way pervasive storage and backup safety controls have develop into, as a part of IT auditing. In actual fact, greater than two-thirds of respondents recognized securing storage and backup being particularly addressed in latest exterior audits.
Abstract and proposals
Contemplating storage and backup compromise are on the coronary heart of all present ransomware kits, absolutely the time has come for us to spice up our information — in addition to our methods — in defending and hardening our storage and backup programs.
Whereas immutability is useful in remediating cyberthreats, it is just the start of a complete cyber resiliency technique.
Based on the analyst agency Gartner:
“Harden the parts of enterprise backup and restoration infrastructure in opposition to assaults by routinely analyzing backup utility, storage and community entry and evaluating this in opposition to anticipated or baseline exercise.”
You wouldn’t dream of not repeatedly scanning your endpoints, OS and community layers for safety dangers. So why wouldn’t you do it on your most vital layer of IT?
This is the reason I like to recommend deploying a vulnerability administration answer that can assist you repeatedly scan your storage and backup programs to mechanically detect safety misconfigurations and vulnerabilities.
These options additionally prioritize dangers so as of urgency and enterprise impression, and a few of them even embrace remediation steerage and auto-remediation options.
The 5 key alternatives for enchancment embrace:
- Assign increased precedence to bettering the safety of enterprise storage and backup programs;
- Construct up information and ability units — and enhance collaboration between your Infosec and IT infrastructure groups;
- Outline complete safety baselines for all parts of storage and backup programs
- Use automation to scale back publicity to threat, and permit way more agility in adapting to altering priorities. Vulnerability administration options can go a protracted method to serving to you cut back this publicity; and
- Apply a lot stricter controls and extra complete testing of storage safety and the power to get well from an assault. This is not going to solely enhance confidence however can even assist establish key information property that may not meet the required degree of knowledge safety.
Doron Pinhas is chief know-how officer at Continuity and co-author of the NIST particular publication, “Safety Tips for Storage Infrastructure.” He has greater than 20 years’ expertise in information and storage administration, mission crucial computing, working system design and growth, cloud computing and networking structure.









/a-7-5bfc2b3c4cedfd0026c10a26.jpg)